Using OpenSSL to create SSL Certificates for vSphere
OpenSSL can be very useful when it comes to working with SSL Certificates in a vSphere environment. It is widely available in Linux/Unix – and that includes the Photon OS in your vCenter. Just be careful!
You should also review the VMware Documentation for vSphere Certificate Requirements for Different Solution Paths to ensure you are using the correct parameters.
Here are a few tidbits I find myself using frequently:
Generate a Private Key
openssl genrsa -out vcenter.key 2048
Creating Certificate Signing Requests
There are 2 parts to this process:
- Create the OpenSSL Config file that describes the certificate properties
- Generate the Certificate Signing Request (CSR) which will be used by your Certificate Authority
Create an OpenSSL config file
This file will be used to generate the Certificate Signing Request (CSR). I keep a copy of this as a template and use that for every certificate I create – replacing the values for each cert.
You can name the file anything you like. For the examples on this page, this file is called vcenter-openssl.cnf
[req] distinguished_name = req_distinguished_name req_extensions = req_ext prompt = no [req_distinguished_name] C = US ST = Ohio L = Columbus O = Cybersylum OU = Cybersylum Labs CN = vcenter.cybersylum.com [req_ext] subjectAltName = @alt_names [alt_names] IP.1 = 172.16.1.32 DNS.1 = vcenter.cybersylum.com DNS.2 = vcenter
Generate the CSR itself
This will read the config file (vcenter-openssl.cnf) and the private key (vcenter.key) and create the CSR (vcenter-openssl.csr)
openssl req -new -key vcenter.key -out vcenter-openssl.csr -config vcenter-openssl.cnf
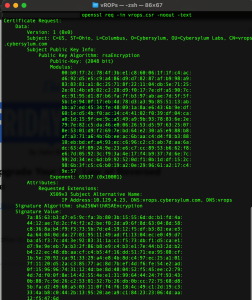
Verifying the contents of the CSR
openssl req -in vcenter-openssl.csr -noout -text
The CSR file is then used with your Certificate Authority to generate the SSL certificate. Typically you will take the SSL Certificate, the private key, and the certificate chain to your target system for import. Different systems handle this in their own way:
Some systems (like the vCenter Machine certificate) will ask for each file separately
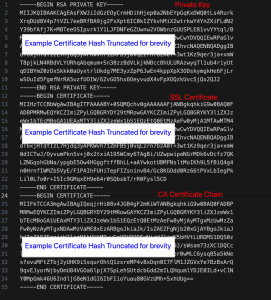
Other systems (vRealize Suite) will ask for a single file that has all 3 pieces combined. Each of these components is just a hash in a text file. You can use copy-paste to combine them into a single file using the editor of choice. The typical order is:
- Private Key
- SSL Certificate
- Certificate Authority chain (can be multiple depending on your CA hierarchy)
An example of this Full Certificate chain would look like this:
Converting a certificate to PEM format
SSL Certificates used in VMware environments need to be in the PEM format. Depending on where your certificate is generated it might be in a different format. For example – the certificate chain from a Microsoft CA can be downloaded in the PKS #7 / .p7b format. In this code example, the original certificate file (certnew.p7b) is converted to the PEM format in the output file (cybersylum-ca-chain.cer).
openssl pkcs7 -print_certs -in certnew.p7b -out cybersylum-ca-chain.cer